Reception immediately following in 3rd floor atrium
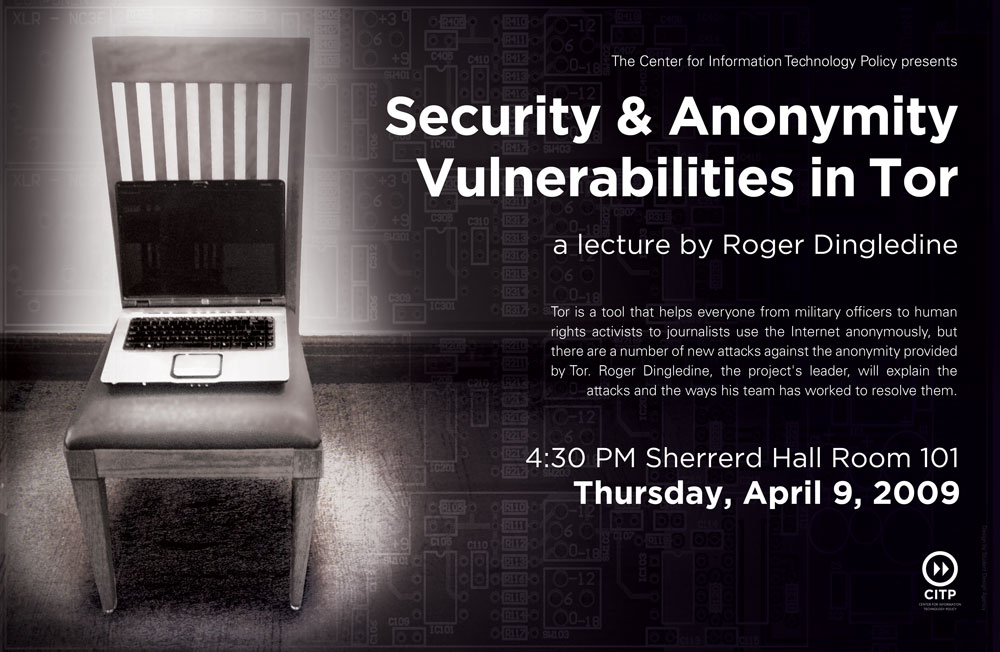
Tor is a tool that makes it easier for people to use the Internet anonymously. Its users range from military officials and police to journalists and human rights activists. There have been a number of exciting bugs and design flaws in Tor over the years, with effects ranging from complete anonymity compromise to remote code execution. Some of them are the programmers’ fault, and some are the fault of components (libraries, browsers, operating systems) that the programmers trusted. Further, the academic research community has been coming up with increasingly esoteric — and increasingly effective! — attacks against all anonymity designs, including Tor.
Roger, who leads the Tor project, will walk through some of the most egregious bugs and design flaws the team has had, and give some intuition about lessons learned building and deploying the largest distributed anonymity network ever. Then he’ll outline the wide variety of current vulnerabilities the project has, explain what they mean for users, and talk about which ones may soon be resolved and which ones will continue to be a pain for the coming years.
Last, he will speculate about categories and topics that are likely to introduce new problems in the future.
Bio:
Roger Dingledine is project leader for The Tor Project, a US non-profit working on anonymity research and development for such diverse organizations as the Electronic Frontier Foundation, the US Navy, and Voice of America. In addition to all the hats he wears for Tor, Roger organizes academic conferences on anonymity, speaks at such events as Blackhat, Defcon, Toorcon, CCC congresses, and What the Hack, and also does tutorials on anonymity for national and foreign law enforcement. Roger was honored in 2006 as one of the top 35 innovators under the age of 35 by Technology Review magazine.